what are the effective responses to a security breach?
Incident Response (IR) is the practice of preparing an organization for the outcome of a security or data alienation through a multitude of ways.
Not every incident is going to be the same and equally such, incident responders must have the ability to react to dissimilar situations. This requires a carefully documented and easily executable programme to allow an organization to chop-chop eradicate malware, ransomware or similar.
Today nosotros're discussing what an effective IR programme looks like and what vital elements can't be disregarded to ensure a successful approach.
A full and detailed analysis of an constructive IR process tin can be found in our Insight Newspaper: "Determining the Effectiveness of an Incident Response Programme"
The 6 Stages of the Incident Response Process
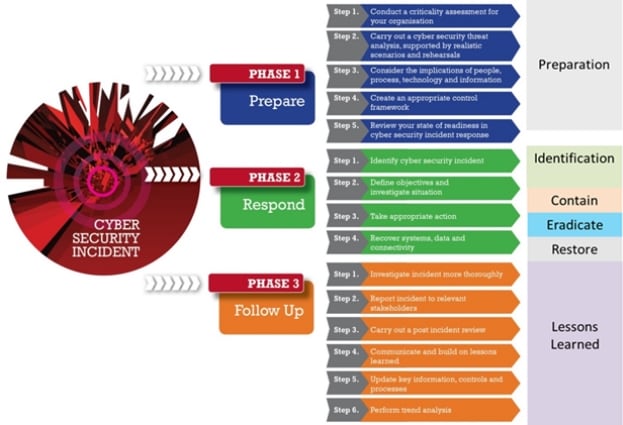
CREST – a non-profit organization providing assurance over the quality of services offered by security firms – has developed a well-defined model for assessing the maturity of each of the half-dozen Incident Response stages.
The graphic below shows how this model addresses controls in vi stages of the Incident Response process. Nosotros are going to look, in detail, at the controls for each of these stages.
Preparation
The key to the training stage is to conduct a careful analysis during false incident tests.
This allows an system to create a carefully synthetic Incident Response timeline with all responsibilities allocated to the well-nigh appropriate stakeholder.
An Incident Response plan should likewise include an assay of the IR resources a company has at its disposal such as port lists, protocol analyzers, network diagrams etc.
This analysis should conclude in the preparation of an IR Tool Kit, fix to employ in the consequence of a alienation.
Identification
An organization should make certain the relative defences are in place to ensure that indicators of compromise are identified.
Such identifiers include:
- Unusual outbound network traffic
- New admin users created
- Anomalies in privileged user account activity (first logon to a arrangement)
- Geographical irregularities (not-standard login attempts)
- Increased database read volume (database dump)
- Large numbers of request for the same file
- Suspicious registry or organisation file changes
- Unexpected patching
- Signs of DDoS activity
If an IT security team doesn't experience like these indicators would show up in their security system, farther review may be required.
Containment
In one case an system is confident that an incident tin/volition be identified, the focus and so turns to containing that incident. An organisation should allocate defined courses of activity based on the potential bear on of diverse incidents.
It needs to examine if it has command of aspects such as the blocking of unauthorized access, blocking of dangerous IP and email addresses or even the isolation of systems on the network amid others. This practice ensures the IT function has complete control and visibility of such actions.
Eradication
The side by side step is to eliminate the crusade of the incident – this stage may overlap with the containment stage.
The aim here is to eradicate the cause, the actual incident and the compromise itself. One time this is washed, it'due south imperative that the eradication is verified (east.k. past monitoring traffic and reviewing critical logs).
The IR procedure should let for eradication steps such as:
- Removing the attack from the network
- Deleting malware
- Disabling breached user accounts
- Identifying vulnerabilities that were exploited
- Mitigating vulnerabilities that were exploited
- Is there a formal process for handling show when dealing with an incident?
- Are there steps to follow to preserve evidence when dealing with the incident?
Restoration
A detailed recovery programme should be prepared and reviewed to determine that all recovery processes are carried out to ensure the restoration of the system as soon as possible, such as: restoring the system from redundancy logs, notifying the relevant stakeholders and addressing like identified vulnerabilities on the network etc.
The restore stage must also consider validating that systems are back to being fully operational and protected.
The IR plan should consider including elements such as an external penetration exam to assess that the restored fixes are sufficient. Consideration should also exist given to the level of detail beingness provided to stakeholders and the timeline for same.
Lessons Learned
This is often considered the most of import stage of the IR process equally lessons learned tin go a long manner to preventing future incidents.
In brusque, this stage involves:
1) Performing a post incident review to identify all the actions taken during the course of the recovery process
2) Formally documenting these lessons, identifying where lessons were learned and communicating these to the relevant stakeholders
3) Updating and amending the existing IR plan to allow for these lessons to be applied to time to come incidents
Conclusion
Although it is non possible to fully prepare for unknown futurity incidents, there are elements of an Incident Response process which require training, to allow effective incident mitigation.
The lesser line is that an Incident Response plan not only needs to be formally defined, simply must exist periodically assessed to ensure it is withal effective.
Applying a well-defined and mature Incident Response framework, similar the one developed by CREST, helps in covering all important aspects of such an assessment.
Source: https://www.bsigroup.com/en-GB/blog/Digital-Trust-Blog/Incident-Response-Process-Explained/
0 Response to "what are the effective responses to a security breach?"
Post a Comment